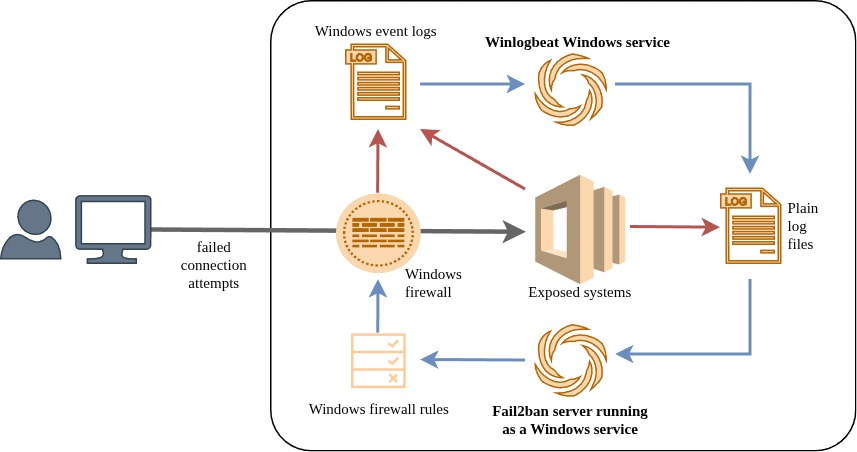
Win2ban integrates:
- Fail2ban for intrusion detection and automated blocking
- Winlogbeat for reliable Windows Event Log monitoring
- Cygwin to provide the required Unix-like runtime environment
- Python and supporting components - preconfigured and bundled
The result is a complete intrusion prevention framework tailored for Windows environments, enabling dynamic firewall rules based on real-time log analysis.
Ideal for securing RDP endpoints, web servers, and other exposed services against brute-force attacks.